No one comes to work expecting a cyberattack, so when one happens it feels random and unpredictable. Responding appropriately is not just the responsibility of the technical specialists, it is a matter of collective leadership of the board, the executives, managers, and other team members.
- The Ponemon Institute discovered that only 47% of organisations have not assessed the readiness of their incident response teams. This means that many companies will only get to test their plans during the worst possible time – the middle of a cyberattack.
- So, how can companies improve their crisis preparedness before a cyberattack happens? Powerful tools include fire drills and table top exercises.
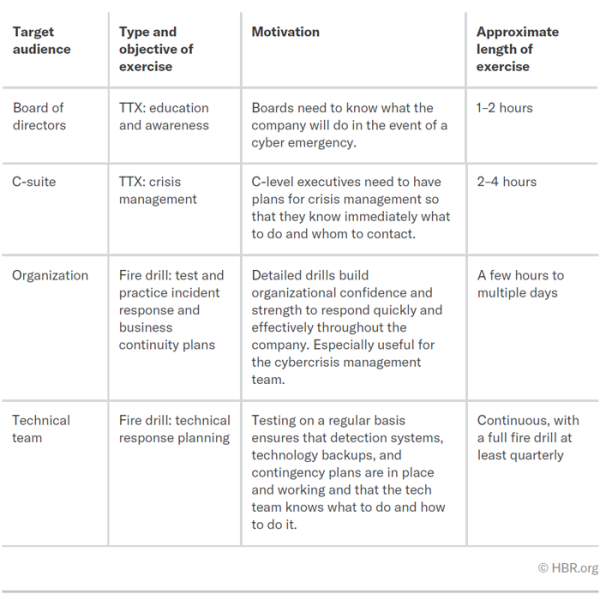
- Fire drills and table top exercises need to be conducted differently depending on the target audience (e.g., the board of directors, c-suite, organisation, or the technical team).
The 4 most effective fire drills and TTXs
From these exercises, companies will likely discover
- Flawed and unmanageable plans that are too long or complex.
- Knowing who to call isn’t always as straightforward as it might seem.
- New unanticipated risks might surface that have been overlooked.
- Impacts of cyberattacks go beyond business continuity and can impact reputation.
- Motivation to invest in cybersecurity can increase.
What should the organisation do next?
- Get the right people in the room.
- Build a scenario timeline of a realistic cyberattack.
- Discuss action plans at each pause of the timeline.
- Create scenarios that involve all team members.
- Practice before the full team exercise.
Why does this matter for businesses?
- Many companies realise that they are unprepared when it’s already too late: in the wake of a cyberattack.
- Unpreparedness can lead to higher recovery cost and a longer time to recover. In other words, it jeopardises resilience.
- Companies can take practical steps to improve their crisis preparedness, and thus their resilience to cyberattack.